All businesses must take steps to protect their data. Whether it’s customer information, financial data, or intellectual property, your company’s data is valuable. Safeguarding this data should be done both through prevention (antivirus, password policies, etc.
Blog
What is MFA and does my small business need it?

Understanding MFA
Multi-factor authentication (or two-factor authentication, abbreviated as 2FA) is an online security layer that requires an additional credential when logging into an account or system. This can include something the user knows (like a PIN), something the user owns (like a phone or key card), or something the user is (like biometric information). This additional layer of security makes it exponentially more difficult for anyone other than authorized users to access sensitive information on your systems.
How many business apps are too many?
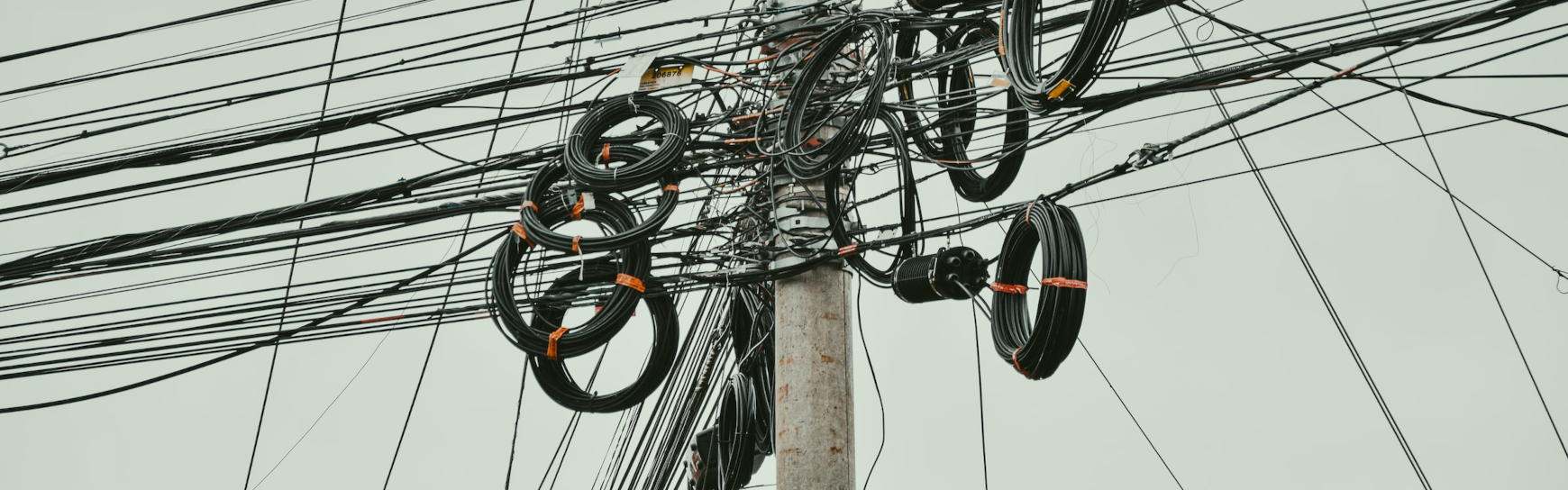
Line-of-business (LOB) applications have changed the way people work, and in many ways these business apps have improved productivity, enabled better engagement with customers, and contributed to a more organized workflow—but at what cost? And how much of a good thing is too much?
Recent surveys have found that many departments run on dozens of different applications, and companies can end up relying on hundreds of apps as a result.
SolarWinds: Lessons for small businesses

It's been over a month and a half since news of the SolarWinds hack started to spread, and the story continues to unfold. Just two weeks ago, a fourth strain of malware was discovered.
While there appears to be much that we don’t know, there are a few familiar themes from this hack that have once again been proven true, and they apply to networks of all sizes.
The vulnerability of distraction
Do what you do best

While it is impractical for most to become so specialized in their careers that they fail to develop general skills, there are many benefits to focusing the majority of your efforts on what you do well. In fact, allowing employees to work on projects that utilize their strengths has been shown to increase their happiness and health.
Feet on the ground, head in the cloud

As cloud computing becomes more prevalent, some companies have begun to question whether there is still a context in which it is practical to purchase a server and locally host line-of-business applications.
Is in-house infrastructure obsolete?
At Team Technology, we are excited about the opportunities provided by cloud hosting, and we have had great success in hosting the infrastructures of some of our clients in our private cloud.
Why hackers target small businesses

One of the assumptions of small-to-medium business owners is that they fly under the radar of most hackers. It's easy to assume that hackers are looking for the biggest payout by targeting the biggest companies. There are several reasons this is simply not the case:
Corporations are getting their acts together
Spending on business security has more than doubled in the last decade.



