Line-of-business (LOB) applications have changed the way people work, and in many ways these business apps have improved productivity, enabled better engagement with customers, and contributed to a more organized workflow—but at what cost? And how much of a good thing is too much?
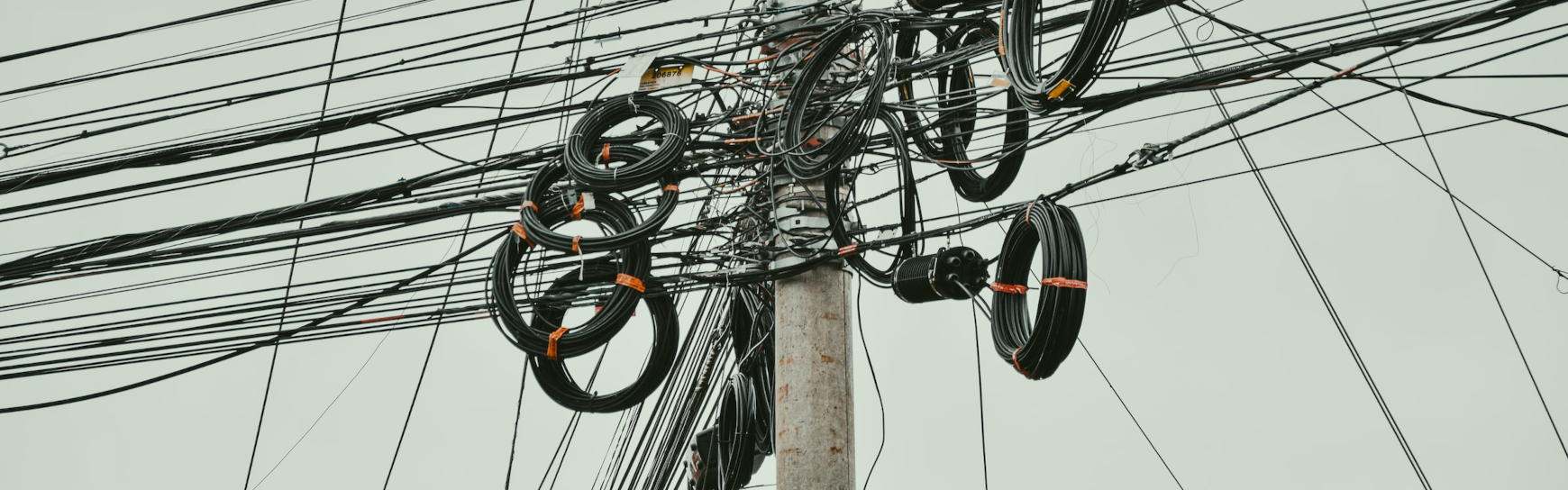
Recent surveys have found that many departments run on dozens of different applications, and companies can end up relying on hundreds of apps as a result.